Choose the Best EAP Plan that’s Right For You
Resource Library
Making Employee Mental Health a Priority
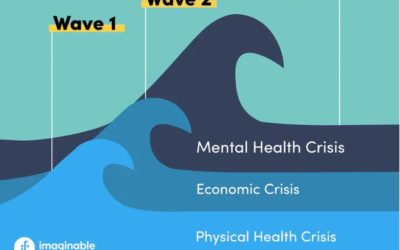
Employee mental health continues to be a front-burner issue in the workplace. We discuss what employers can do to help their employees navigate persistent post-pandemic mental health challenges. Four years ago in March, the World Health Organization declared that...
HR News Roundup: Trust, Taboo Topics, Talent & More
Your employees may not trust you. Here’s what HR can do Tom Starner, Human Resource Exeutive As global uncertainty continues to affect organizations and their workforces, trust in the workplace is needed more than ever—but leaders appear to have significant work ahead...
Key April dates for employee communications
Planning upcoming employee communications? See our list of key April dates & events, along with links to helpful resources. ESI EAP employee members also have access to counseling, coaching and a wealth of online self-help resources, including webinars, health...
Resource Library
Making Employee Mental Health a Priority
Employee mental health continues to be a front-burner issue in the workplace. We discuss what employers can do to help their employees navigate persistent post-pandemic mental health challenges. Four years ago in March, the World Health Organization declared that...
HR News Roundup: Trust, Taboo Topics, Talent & More
Your employees may not trust you. Here’s what HR can do Tom Starner, Human Resource Exeutive As global uncertainty continues to affect organizations and their workforces, trust in the workplace is needed more than ever—but leaders appear to have significant work ahead...
Key April dates for employee communications
Planning upcoming employee communications? See our list of key April dates & events, along with links to helpful resources. ESI EAP employee members also have access to counseling, coaching and a wealth of online self-help resources, including webinars, health...
Sober curious? We’ve got resources to help
April is National Alcohol Awareness Month, a good time to think about your drinking and the impact on your overall health and well being. If you're sober-curious, we have some resources to help. Gallup has tracked Americans use of and attitudes towards alcohol for...